Walk into a busy hotel or a corporate office during rush hours. The scene repeats itself. A line at the entrance. The staff is trying to keep up. Details are getting written manually while people wait.
The delay starts early. And that delay shapes the entire experience.
For most businesses, this is where both efficiency and user experience start slipping.
Guest identification no longer sits in the background as a basic process. It has moved to the front. The first interaction. The first impression.
A slow check-in creates friction. People notice it.
A fast, seamless flow does the opposite. It builds confidence within seconds.
The shift is clear. Businesses are no longer satisfied with systems that only record information. They want systems that respond, adapt, and improve how people move through their spaces.
If you plan to develop a guest identification system, the focus needs to go beyond basic functionality. Speed matters. Security matters. But long-term value comes from scalability and adaptability.
Facial Recognition and Guest Identification: Market Overview & Stats
Facial recognition is no longer treated as an advanced add-on. It has moved closer to being a default layer in modern systems. The reason is simple. Manual checks slow things down. Traditional digital systems lack intelligence. Businesses want accuracy without adding friction. The numbers reflect this shift.
The global visitor management system market is expected to grow from USD 1.8 billion in 2026 to USD 6.9 billion by 2036, with a CAGR of 11.7%. This growth points to a clear demand for real-time monitoring and touchless entry systems.
Facial recognition is expanding at an even faster pace. The market is projected to reachUSD 36.2 billion by 2035, growing at a CAGR of 16.1%. Security, access control, and identity verification are driving this adoption.
A few patterns are shaping this space:
- Rapid growth of guest management systems
Businesses are replacing manual processes with automated identification. This is visible across offices, hospitals, and hotels where managing high visitor volume is critical. The goal is to reduce delays and improve flow without increasing staff load. - Shift toward web-based and cloud platforms
Systems are moving online. This allows real-time access and easier scaling across locations. Teams no longer depend on isolated systems. Everything connects and updates instantly. - Facial recognition as a core AI layer
It plays a central role in identification. From surveillance to access control, facial recognition is being used to reduce manual effort and improve accuracy. - Adoption across BFSI and enterprise environments
Sectors with strict security needs are leading the shift. Compliance, risk control, and identity verification are pushing for faster adoption. - Move toward contactless experiences
Touch-free systems are becoming standard. They reduce friction and improve safety at the same time.
Another change is happening quietly. AI models are improving over time. Systems are learning from data. Recognition becomes more accurate. False matches reduce. Performance adapts to real-world conditions.
This is no longer about installing a tool. Businesses are building connected ecosystems where identification systems support both operations and experience.
From Visitor Logs to Intelligent Systems: The Evolution of Guest Identification
Guest identification did not change overnight. It moved step by step.
Earlier systems relied on manual logs. These were slow. Errors were common. There was no visibility beyond basic records. Then came digital systems. Data moved to screens. Speed improved. But the system remained static. Information was stored, not used.
Now the direction is different.
Modern systems process data in real time. They do more than record identity. They interpret it.
| Stage | Key Limitation | Modern Upgrade |
| Manual Logs | Delays, errors, no visibility | Digital capture |
| Digital Systems | Static records | Automated workflows |
| AI-Based Systems | — | Real-time intelligence |
Today, systems track patterns. They identify repeat visitors. They support personalization. The role has expanded.
What Is a Guest Identification System (From a Business Perspective)?
A guest identification system is a digital framework that verifies and manages visitor identity across entry points. From a business view, its role is broader.
It connects operations with experience.
On one side, it controls access and ensures security. On the other hand, it reduces friction for users moving through the system.
Every system answers three questions:
- Who is the guest
- Should access be allowed
- How can the interaction improve
When businesses plan to develop a guest identification system, the focus should include speed, decision-making, and user flow. Verification alone is not enough.
Why Businesses Are Investing in Smart Guest Identification Systems
The investment is driven by clear outcomes.
- Operational efficiency
Manual processes increase workload. Teams spend time on repetitive tasks. Automation reduces this effort and improves flow across entry points. - Security control
Real-time verification helps detect risks early. Alerts and validation layers reduce the chances of unauthorized access. - User experience
People expect faster entry. Delays create frustration. A smooth system improves satisfaction without extra effort. - Data-driven decisions
Modern systems capture behavioral data. This helps businesses identify patterns, plan resources, and improve services over time.
Core Components That Make a Guest Identification System Work
A system like this does not run on a single layer. It depends on multiple connected components.
- Data Capture Layer
This is where information enters the system. Cameras, kiosks, mobile apps, and web interfaces collect data in real time. The focus is on accuracy without slowing down the process. - Processing Layer
Captured data moves here. AI models verify, clean, and prepare it. This layer ensures that the system works with reliable inputs. - Decision Layer
Access decisions happen here. The system compares incoming data with stored records and predefined rules. Based on this, entry is allowed or denied. - Experience Layer
This is what users interact with. Dashboards, notifications, and interfaces sit here. The goal is to keep the experience smooth for both staff and visitors.
How AI Transforms Guest Identification Systems
Identification systems no longer depend on manual validation. That shift happened when AI entered the process.
Instead of checking IDs or verifying entries step by step, systems now interpret data instantly.
Facial recognition plays a major role here. A face is captured. The system compares it within seconds. No physical interaction is required. No delay at the entry point.
Machine learning works in the background. It studies patterns from repeated usage. Over time, recognition improves. Errors reduce. Accuracy increases with real-world exposure.
Natural language processing adds another layer. It reads documents. Extracts key information. Converts unstructured input into usable data without manual effort.
There is also a security angle. AI tracks behavior. If something unusual appears, the system flags it immediately. This could be an unexpected access attempt or a mismatch in identity patterns.
The real shift is not speed alone. It is adaptability.
The more the system is used, the sharper it becomes. This continuous learning cycle is what separates modern solutions from older, rule-based systems.
How a Modern Guest Identification System Actually Works
From the outside, the process looks quick. Almost invisible.
Inside, multiple actions run at the same time.
A guest walks in or opens a mobile interface. Data gets captured. This could be through a camera, a document scan, or a simple input form.
That data does not sit idle. It moves instantly.
The system analyzes it. Matches it against stored records or external databases. This happens in real time, without interrupting the user flow.
Once the match is confirmed, a decision follows. Access is either granted or restricted.
At the same moment, the system logs the interaction. This builds a record for future reference.
If something feels off, alerts are triggered. No manual monitoring needed.
All of this happens within seconds. That speed is what defines the reliability of a modern guest identification system.
Types of Guest Identification Methods (With Use Case Fit)
Different environments demand different approaches. One method does not fit all.
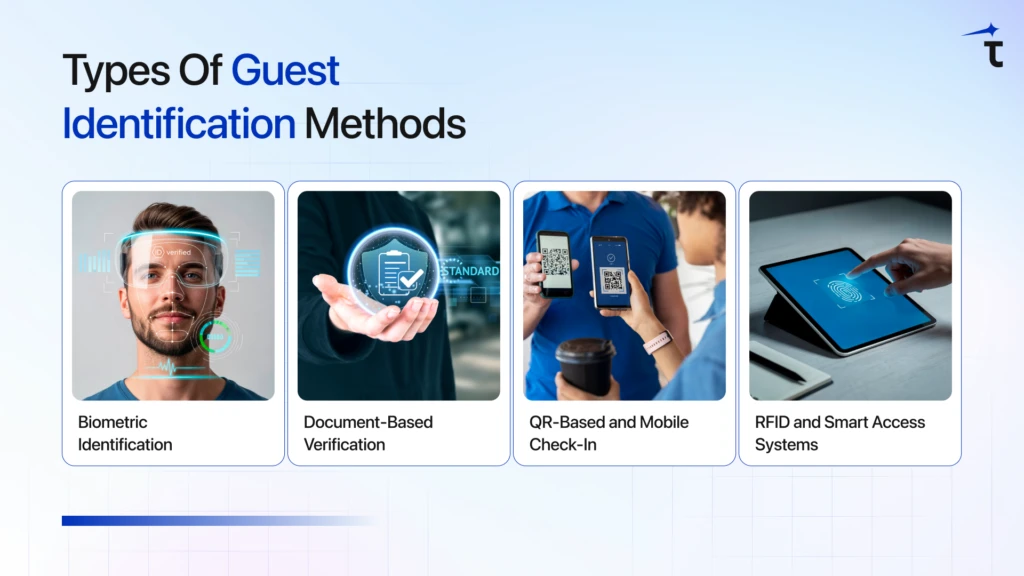
- Biometric Identification
This method uses physical traits like facial structure or fingerprints. It reduces dependency on cards or documents. Entry becomes faster and more secure. High-security zones often rely on this approach because accuracy matters more than convenience. - Document-Based Verification
IDs such as passports or licenses are used here. The system validates authenticity and extracts data. This method fits industries where documentation is mandatory, especially in travel and hospitality setups. - QR-Based and Mobile Check-In
Users verify identity through their phones. A QR code handles entry. This reduces waiting time and removes physical contact points. Events and large gatherings often prefer this model for faster movement. - RFID and Smart Access Systems
Access is controlled through cards or wearable devices. These systems are common in offices and large facilities where repeated entry is required. They offer consistency and ease of use for regular visitors.
Step-by-Step Process to Develop a Guest Identification System
A system like this does not come together by stacking features. It comes from decisions made in the right order. Skip that, and you end up rebuilding half of it later.
If you plan to develop a guest identification system, treat it like a sequence, not a checklist.
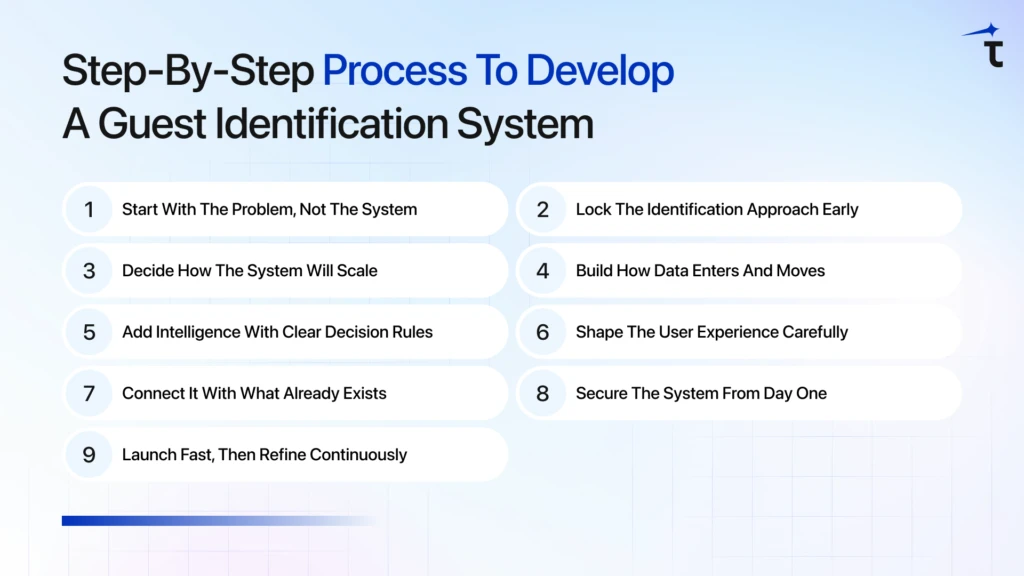
Step 1: Start With the Problem, Not the System
Before thinking about tools or tech, define the situation.
Where will this system run? A hotel lobby behaves differently from a hospital entry. A corporate office has its own flow.
Now narrow it down.
Is the issue long queues?
Is it weak access control?
Is it a lack of visibility?
Set 2–3 clear outcomes. For example:
- Reduce check-in time
- control unauthorized access
- track repeat visitors
This step filters everything that follows. Without it, features pile up without purpose.
Step 2: Lock the Identification Approach Early
This decision shapes the entire experience.
You have options. Biometrics. Documents. QR-based entry. Mobile-first flows.
Each comes with trade-offs.
Biometric systems reduce manual work but need a strong infrastructure.
QR and mobile flows move faster but depend on user participation.
Document verification fits compliance-heavy environments.
In many cases, one method is not enough. Combining two approaches often works better, especially when both speed and control matter.
Step 3: Decide How the System Will Scale
This is where most systems fail later.
Think beyond current usage. What happens when traffic doubles? Or when multiple locations are added?
You need to choose the foundation:
- cloud-based for flexibility
- on-premise for control
- hybrid for balance
This is not just a tech decision. It affects cost, performance, and maintenance.
A weak architecture does not show problems immediately. It breaks under pressure.
Step 4: Build How Data Enters and Moves
Everything depends on this layer.
Data can come from anywhere. Cameras. Kiosks. Mobile apps. Web forms.
The challenge is not capture. It is speed and accuracy together.
Once data enters, processing starts instantly:
- identity validation
- OCR-based extraction
- pattern matching
If this pipeline slows down, the entire system feels broken. Even if everything else works.
Step 5: Add Intelligence With Clear Decision Rules
Now the system needs to think.
AI handles recognition. It improves matching over time. It spots patterns that manual systems miss.
But AI alone is not enough.
You need fixed logic as well:
- When to allow access
- When to stop it
- When to trigger alerts
If rules are unclear, decisions become inconsistent. That creates risk.
This is the point where the system shifts from reactive to responsive.
Step 6: Shape the User Experience Carefully
Most systems fail here, not in the backend.
If the process feels slow or confusing, users resist it. Staff bypass it.
Keep the flow tight:
- fewer steps
- clear prompts
- minimal input
A guest should not think twice while using it.
A staff member should not need training to operate it.
Speed is not just technical. It is also about perception.
Step 7: Connect It With What Already Exists
An isolated system creates more work, not less.
It needs to link with:
- CRM platforms
- booking systems
- access control tools
- internal dashboards
This removes duplication. Data flows automatically.
It also opens up new use cases. Analytics. Personalization. Reporting.
Without integration, the system stays limited.
Step 8: Secure the System From Day One
Security cannot be patched later.
You are dealing with identity data. That raises the stakes.
Focus on:
- encryption
- access control layers
- secure storage
Compliance also matters. Regulations like GDPR are not optional in many cases.
If users feel their data is not safe, adoption drops. Trust is hard to rebuild once lost.
Step 9: Launch Fast, Then Refine Continuously
Do not aim for perfection before release.
Test the system in real conditions:
- peak hours
- different user types
- edge cases
Fix what breaks. Then deploy.
After launch, the real work starts.
Track usage. Monitor errors. Improve accuracy. Adjust flows.
A guest identification system is not static. It improves with usage. The systems that evolve stay relevant. The ones that don’t fall behind quickly.
Real-World Use Cases Across Industries
You see these systems in more places than you notice.
A hotel lobby during peak check-in hours. Guests arrive together. No one wants to wait. A fast identification system keeps the line moving and allows staff to focus on service instead of paperwork. Walk into a corporate office. Security matters more here. Every visitor needs to be verified before access is granted. The system handles that quietly in the background.
Now think about a hospital. Accuracy becomes critical. A small mismatch can create bigger issues. Identification systems help ensure the right patient is linked to the right records.
At large events, the challenge shifts again. Volume increases. Entry needs to stay smooth even when hundreds arrive at once. Systems manage flow without creating bottlenecks.
In financial institutions, the focus tightens further. Fraud prevention. Identity validation. Every interaction needs an extra layer of verification.
Different environments. Different pressures. But the purpose stays consistent. Keep operations smooth. Keep access controlled.
Cost Breakdown: What Impacts the Development Budget
There is no single price for this. The cost to develop a guest identification system depends on how far you want to take it. A simple setup with basic check-in features costs less. Add AI, real-time processing, and integrations, and the numbers change quickly. Most businesses fall somewhere between $15,000 and $120,000+. The gap exists for a reason.
A smaller setup works for limited usage. One location. Fewer users. Basic validation.
A larger system handles multiple locations, high traffic, and deeper intelligence. The mistake many teams make is starting too big.
Instead, match the system with your actual need. Build what is required now. Expand later. Here is how the cost typically breaks down:
| Component | Basic System ($15K–$30K) | Mid-Level System ($30K–$70K) | Advanced System ($70K–$120K+) |
| Identification Method | QR / Manual Entry | Document + OCR | Facial Recognition + Biometrics |
| AI Capabilities | Minimal | Basic automation | Advanced ML & real-time detection |
| UI/UX Design | Standard interface | Customized dashboards | Fully optimized, multi-device UX |
| Integrations | Limited | CRM / Booking systems | ERP, IoT, multi-system integrations |
| Security Features | Basic encryption | Role-based access | Advanced security + compliance layers |
| Scalability | Single location | Multi-location | Enterprise-level scalability |
A better approach is to start focused. Build a working version. Then scale based on usage and feedback. This keeps costs controlled and avoids rebuilding later.
Future Trends: What Will Define Guest Identification in 2026
The future of guest identification is moving toward systems that are faster, smarter, and more adaptive. Businesses are no longer focusing only on verification. The shift is toward creating connected experiences where identification, security, and personalization work together in real time.
Contactless and Frictionless Identification
Physical interaction is reducing. Users prefer quick entry without touching screens or handing over documents. Facial recognition and mobile-based access are becoming standard in many environments.
Behavioral Biometrics
Identification is moving beyond physical traits. Systems are starting to read patterns. Typing speed. Movement. Interaction style. This adds another layer of validation without slowing the user.
AI-driven Personalization
Identification does not stop at verification anymore. Systems remember past interactions. They adjust based on user behavior. This helps businesses deliver more relevant experiences without manual input.
Integration with Connected Environments
Systems are no longer standalone. They link with IoT devices and smart infrastructure. Entry, access, and environment settings start working together.
Blockchain-based Identity Systems
Data control is becoming a concern. Blockchain introduces a model where identity data is secure and harder to alter. It also gives users more visibility into how their data is used.
The pattern is clear. Identification systems are turning into connected layers within a larger ecosystem.
Conclusion
Guest identification has evolved into a core part of how modern businesses operate. It is no longer limited to verifying identity. It now plays a direct role in improving security, reducing operational delays, and shaping user experience from the very first interaction. From choosing the right technology to building scalable architecture, every step in guest identification system development contributes to long-term efficiency and growth.
As businesses plan to develop a guest identification system, the focus should stay on building solutions that are flexible, secure, and aligned with real user needs. With the right approach and execution support from TechnoYuga, you can create systems that go beyond identification and deliver meaningful impact. The goal is not just to recognize guests, but to create smoother, smarter, and more connected experiences at every touchpoint.
FAQs
A guest identification system captures and verifies visitor data using methods like biometrics, QR codes, or document scanning. The system processes this data instantly and decides access in real time.
Costs usually range from $15,000 to $120,000+, depending on features, AI usage, integrations, and scale. Simpler systems stay on the lower end, while advanced setups require higher investment.
There is no single answer. Facial recognition, OCR, and mobile-based verification are common options. Many businesses combine methods to balance speed, accuracy, and security.
Most systems take between 2 to 6 months. The timeline depends on complexity, integrations, and customization requirements.
Security depends on implementation. Strong systems use encryption, controlled access, and compliance frameworks to protect sensitive data.